List
10 Types of Hacking Techniques You Should Know About

With a few hacks, hackers are able to discover your private unauthorized information that you do not wish to share.
Be aware of common hacking methods, such as phishing DDoS clickjacking. can help you with your safety.
In light of these, it is important to understand the hacking techniques commonly employed to obtain your personal data in a non-secure manner.
10. Keylogger
Keylogger is a basic application that tracks the keystrokes and strokes you type to a log file that is stored on your computer. The log files could contain your personal email addresses and passwords. Also known as keyboard capturing it could be hardware or software.
Keyloggers that are software-based target software that is installed on computers and hardware devices focus on keyboards and electromagnetic emissions, smartphones, sensors, etc.
Keylogger is among the major reasons why banks online offer the option of using keys that they simulate. When you’re using your computer in a public space be sure to exercise extra precautions.
9. Denial of Service (DoS\DDoS)
The Denial of Service attack is an attack that hacks the server or website offline by flooding the website or server with an enormous amount of traffic until the server cannot handle all requests at the same time and eventually it shuts down.
This is a well-known technique where hackers flood the machine targeted with a plethora of requests that overburden the system that, in turn, hinder the requests that are actually executed.
In DDoS attacks, hackers typically use zombie computers or botnets which are designed to perform one function and that is to overwhelm your system with requests packets. Every year, as cybercriminals and their methods, are getting more sophisticated the number of DDoS attacks continues to grow.
8. Waterhole attacks
If you’re a huge enthusiast of Discovery or National Geographic channels, you might be familiar with waterholes that have been hacked. To poison a spot it is necessary that the hacker targets the physical location that is most easily accessible for the target.
For instance, if you are in the vicinity of where a river’s water is poisoned, it can affect the entire area of animals in summer. Similar to this hackers will target the most frequented physical locations in order to target the victim. It could be a cafeteria.
If the hacker becomes aware of your location and your location, they could use this method of attack to build an untrue Wi-Fi access point. This allows them to modify your most popular website to redirect them to your site to obtain your personal details.
Since this attack gathers data about a person from a particular location it is much more difficult. The best way to safeguard yourself against such attacks is to practice fundamental security rules and ensure that your OS/software is up-to-date.
7. Fake WAP
For amusement, hackers can make use of software to create a wireless access point. The fake WAP is connected to a public WAP. After you are connected with the fake network hackers can gain access to your personal information, as in the above scenario.
It’s among the easiest hacks you can do and only requires a single program and a wireless network in order to perform it. Any wireless network can be identified with a legit name, such as “Heathrow Airport WiFi” or “Starbucks WiFi” and begin spying on you. A great way to safeguard yourself from attacks like this is to use a reliable VPN provider.
6. Eavesdropping (Passive Attacks)
In contrast to other attacks that are active by using an attack that is passive hackers can observe the computers and networks to obtain unwanted information.
The reason for the eavesdropping process is not to harm the system but rather to gain the information you need without being detected. These hackers could attack instant messaging, email services, telephone calls, web browsing, and various other ways of communicating.
The people who participate in these actions are usually cyber criminals who have been classified as black hats, governments, etc.
5. Phishing
Phishing is a technique for hacking where a hacker replicates the most visited websites and then entices the victim by sending a fake link. In conjunction, together with the use of social engineering, this becomes an extremely frequently utilized and most deadly attack.
When a victim attempts to log in or input details, hackers gain the personal details of the victim by using the trojan on the fake web. Phishing through iCloud and Gmail account was the primary attack technique used by hackers that focused on the “Fappening” leak that involved a number of Hollywood female stars.
4. Virus, Trojan, etc.
Trojans and viruses are harmful software programs that are installed in the victim’s system. They continue to transmit the victim’s data to hackers.
They also have the ability to lock your files, display fraud advertisements, redirect traffic, monitor the data of your computer, and even spread to all the computers that are connected to the network.
It is possible to read about the differences and comparisons between different worms, malware trojans, and more. For more information, click here.
3. ClickJacking Attacks
ClickJacking may also go under another term, UI Redress. In this type of attack, the hacker hides the actual UI on which the victim should click. This kind of behavior is common for in-app downloads or movie streaming torrent sites. Although they typically employ this tactic to generate advertising dollars, some may make use of it to steal personal data.
In the case of this kind of hacking, the hacker hijacks actions of the victim’s clicks that aren’t intended for the specific webpage, but instead for an alternative page to where the hacker would like the victim to go. The trick is to fool users on the internet to perform an unintentional action by clicking on a hidden link.
2. Cookie theft
Cookies in our browsers save personal information such as the history of our browsing, usernames, and passwords for various websites that we use. If the hacker gains access to your cookies and authenticates himself as you using the browser. One method used to attack is to modify the user’s IP packets so that they be able to pass through the attacker’s computer.
Sometimes referred to as SideJacking and Session Hijacking, this attack is simple to execute in the event that the user is not employing SSL (HTTPS) to secure the duration of the session. When you visit websites on which you input your password as well as banking information, it’s essential to ensure that their connections are secure.
1. Bait and Switch
Utilizing the Bait and Switch hacking technique an attacker is able to purchase ads on websites. Then, when a person clicks on the advertisement and is taken to a website affected by malware.
This is how they are able to continue to install malware and adware onto your system. The links to download and advertisements that are displayed in this method are attractive and the users are expected to click on the identical.
The hacker may use malicious software that is believed by the user as authentic. After installing the malware on your computer, the hacker gains the computer with no access rights.

-

 List7 months ago
List7 months ago1337x Proxy List For 2022 [100% Working 1337x Mirror Sites]
-

 Explained7 months ago
Explained7 months agoWhy Did iMessage Turn Green Explained!
-

 How Tos7 months ago
How Tos7 months agoHow To Get A Specific Phone Number for yourself?
-
 List2 years ago
List2 years ago11 Best Music Players for Android Auto
-

 Explained7 months ago
Explained7 months agoHow Can Monitors Be Connected By USB? (Explained)
-

 Explained7 months ago
Explained7 months agoWhat is Android System WebView? Should You Delete it?
-
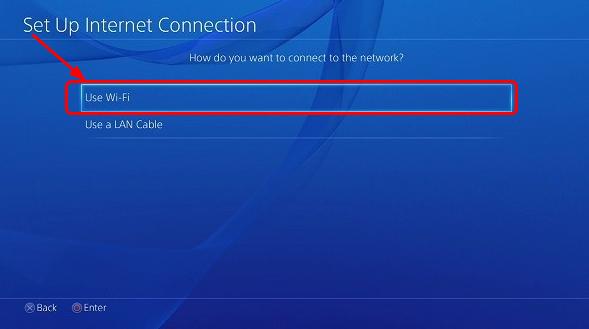
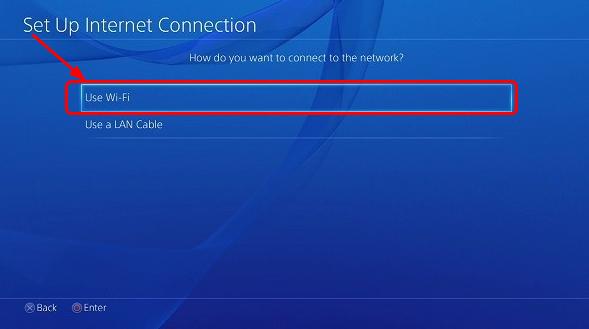 Gaming7 months ago
Gaming7 months agoWhy Can’t I Connect to 5GHz WiFi On PS4? [Solved!]
-
 How Tos7 months ago
How Tos7 months agoHow To Fix This Webpage Is Not Available Error In Google Chrome